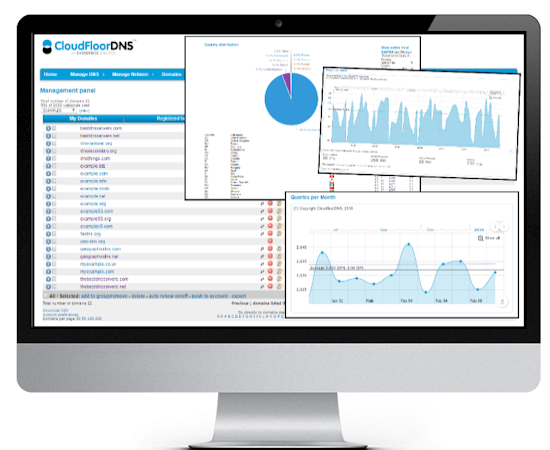
Managed DNS that provides fast, reliable Anycast DNS with a 100% uptime SLA & DDoS mitigation.
Managed DNS
Managed DNS
Global Anycast DNS
DNSSEC
Secondary DNS
Secondary DNS
Backup your DNS Zones
100% Uptime SLA
Domains
Domains and SSL
Domain & DNS API
Brand Management
DNS Failover
DNS Failover
ISP Failover
CNAME Failover
GEO DNS
Simple GEO DNS
GEO VPN
GEO GSLB